There are times when you might want to hide one or more of your windows drives because of security reasons (children getting up on the system and messing up everything or if the computer is in use by multiple people). For theses reasons, you would just prefer to hide your data in a safe place and if one of your drives is full of sensitive information, you would rather hide the drive from My Computer.
There are two ways of doing it, one from the group policy editor and the second from registry editor. I will explain both of them here:
1-Hiding drives using Group Policy Editor
Go to Start –> Run –> gpedit.msc
The group policy editor will open. Go to the following node:
User Configuration –> Administrative Templates –> Windows Components –> Windows Explorer
Now go to the right hand window and double click the value “Hide these specified drives in My Computer”, select enable and select the drives from the drop down menu.
This is restrictive in the sense that it only specifies drives up to D drive. Or all the drives can be hidden.
2-Hiding the drives using Registry Editor
To open the registry editor
Go to Start –> Run –> regedit
Go to HKEY_LOCAL_MACHINE\SOFTWARE
\Microsoft\Windows\CurrentVersion\policies\Explorer
In the right hand pane, right click –> new –> DWORD Value
Rename it to “NoDrives” (without quotes)
To calculate the value, add together the numbers for the drives you want to hide, using the formula: A=1, B=2, C=4, D=8, E=16, F=32, G=64, H=128, I=256 and so on. Put the result in the NoDrives key value. Remember to select decimal instead of HEX from the NoDrives key. For Example if I want to hide C and F drives, C+F = 4+32 = 36. Put the value 36 in NoDrives key.
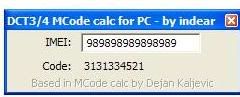
Alternatively, you can use NoDrives!!! (NT Drive Calculator) for calculating the drive values. It’s a lot easier than calculating by hand.
Note: Always use the registry editor with caution because, if used inappropriately, it can mess up the whole system. I recommend creating a restore point before getting your hands on the registry editor.
 Ulisess Seguridad 9.91 "12 MB"
Ulisess Seguridad is a collection of cracks/fixes released till date for NOD 32 antivirus and ESET smart security 32BIT & 64BIT.
Ulisess Seguridad 9.91 "12 MB"
Ulisess Seguridad is a collection of cracks/fixes released till date for NOD 32 antivirus and ESET smart security 32BIT & 64BIT.